Hacking together runtime policy enforcement for agents last week reminded me of something the Linux…
Hacking together runtime policy enforcement for agents last week reminded me of something the Linux security community learned over 20 years.
The architecture is the easy part. Tuning is what kills you.
NVIDIA's new OpenShell has the right design. Out-of-process enforcement. Kernel-level sandbox. Nothing the agent does works unless a YAML policy explicitly allows it.
That's the strict mandatory access control model the NSA built. But when Fedora tried shipping it to regular users, the SELinux team abandoned it because enforcing a single strict policy across diverse environments "was not feasible."
What survived was targeted enforcement. RHEL only confines high-risk daemons. Ubuntu's AppArmor guards a handful of services. Everything else runs unconfined. MAC won after it stopped trying to govern everything.
OpenShell is a bet on that same model that didn't survive contact with users.
It might work because the scope is narrower: one agent's tool calls, not every process on an OS. But every new tool and workflow is a new policy rule to maintain, and every false positive is a moment where someone chooses between tuning the policy or loosening it to ship.
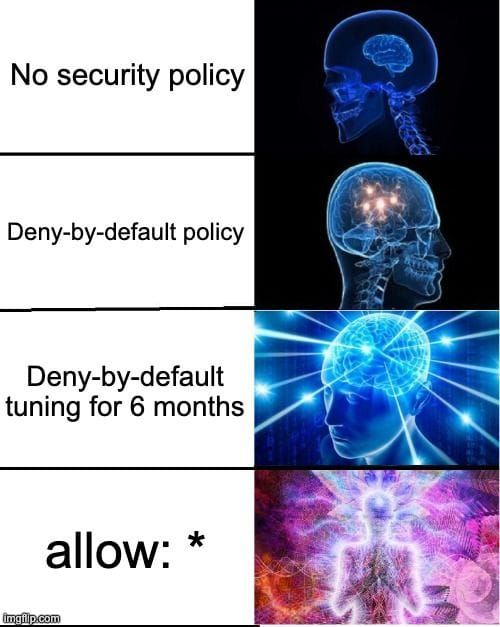
This is the Tuning Tax. The same force that made disabling SELinux the industry's most popular troubleshooting step.
What's the tightest runtime policy you've maintained for more than six months without someone quietly loosening it?

